Exactly how CSRF Attacks Are Executed: Real-World Examples
Cross-Site Request Forgery (CSRF) attacks are a kind of security weeknesses which could have considerable implications for internet applications. CSRF episodes exploit the believe in that a web program has in some sort of user’s browser by tricking the browser into making not authorized requests for the user. Understanding exactly how CSRF attacks are usually executed and evaluating real-world examples can easily help developers and even security professionals mitigate these threats successfully.
Understanding CSRF Problems
CSRF attacks occur when a harmful actor tricks a person into performing actions on a web application where that they are authenticated, with out their consent. These kinds of actions may range coming from changing account adjustments to making not authorized financial transactions. The important thing to a successful CSRF attack is the exploitation regarding the trust which a web application features in the user’s browser. When a new user is logged into a internet application, their internet browser automatically sends authentication cookies or bridal party with every demand. Attackers leverage this kind of behavior to their own advantage.
Execution regarding CSRF Problems
Discovering Vulnerable Endpoints:
Attackers first identify internet application endpoints of which perform actions in behalf of authenticated users. These endpoints are usually accessible by means of HTTP POST or even GET requests. Typical targets include types for updating user information, transferring finances, or changing account settings.
Crafting Malicious Requests:
Once susceptible endpoints are recognized, attackers craft destructive requests that imitate legitimate requests. These kinds of requests include almost all necessary parameters and data to conduct the desired activity. Attackers can add these requests in several ways, such while through malicious sites, emails, or actually social media posts.
Exploiting User Discussion:
Attackers need to be able to trick the customer into interacting with the particular malicious request. This kind of can be attained by embedding the request within an photo, link, or hidden form on a web page controlled by the attacker. When the particular user visits typically the malicious webpage, the particular browser automatically delivers the crafted obtain to the prone web application, together with the user’s authentication bridal party.
Real-World Examples associated with CSRF Attacks
Illustration 1: Changing Customer Email Address
In a new real-world scenario, an attacker may target a web program that allows users to update their emails. The susceptible endpoint might appear like this:
makefile
Copy code
ARTICLE /update-email HTTP/1. a single
Host: vulnerable-website. apresentando
Cookie: session=abc123
Content-Type: application/x-www-form-urlencoded
email=new-email@example. possuindo
The attacker crafts a malicious website containing the next HTML form:
code
Copy code
Whenever the user, that is logged into the particular vulnerable website, visits the malicious web page, the proper execution is instantly submitted, changing the particular user’s email tackle to the attacker’s email address with out the user’s information.
Example 2: Unauthorized Fund Move
One other common target with regard to CSRF attacks is usually financial transactions. Look at a banking application with an endpoint for transferring money:
makefile
Copy signal
POST /transfer-funds HTTP/1. 1
Host: banking-website. apresentando
Cookie: session=xyz789
Content-Type: application/x-www-form-urlencoded
amount=1000&account=attacker-account
The attacker products a malicious e-mail containing an image tag:
html
Copy code
When the consumer opens the electronic mail, the browser makes a GET ask for to the WEB ADDRESS specified in typically the image tag, shifting funds from typically the user’s account to the attacker’s accounts.
Mitigating CSRF Assaults
To protect in opposition to CSRF attacks, developers can implement several mitigation strategies:
Anti-CSRF Tokens:
The most successful defenses against CSRF attacks is the employ of anti-CSRF tokens. These tokens are usually unique for each and every session and are usually included in forms and requests. The server validates typically the token before running the request, ensuring that the request originated from a trusted source.
important link :
Placing the SameSite characteristic on cookies can restrict how biscuits are sent with requests. By establishing the attribute to Strict or Locker, cookies will only be sent along with requests received from the same site, stopping cross-site requests coming from including the snacks.
Referer and Origin Header Validation:
Web servers can check typically the Referer or Origin headers to make certain typically the request originated from a trusted source. Although it is not foolproof, this can easily offer an additional layer of security.
Customer Interaction Validation:
Requiring additional user connection, such as entering a password or resolving a CAPTCHA, just before performing sensitive steps can assist prevent computerized CSRF attacks.
Conclusion
CSRF attacks pose a tremendous threat to web applications, exploiting the trust between a user’s browser as well as the web app. By understanding just how these attacks are executed and reviewing real-world examples, programmers and security experts can better safeguard their applications. Employing mitigation strategies these kinds of as anti-CSRF tokens, SameSite cookies, referer validation, and end user interaction validation may significantly reduce typically the likelihood of CSRF assaults, ensuring a even more secure web experience for users.
Precisely how Cross-Browser Testing Increases Web Accessibility
In an era where digital existence is crucial with regard to businesses and companies, ensuring that internet sites are accessible in order to everyone—regardless of their browser or device—is a fundamental aspect regarding web development. Cross-browser testing, a critical element of web advancement, plays a substantial part in enhancing web accessibility. This informative article explores how cross-browser tests contributes to producing an inclusive internet environment, the problems involved, and finest practices for powerful testing.
Understanding Net Accessibility
Web accessibility refers to the practice of making websites usable by people of most abilities and afflictions. The goal is to make certain that persons with visual, auditory, physical, or intellectual impairments can gain access to and interact with site content effectively. Crucial guidelines for internet accessibility include typically the Web Content Availability Guidelines (WCAG), which in turn provide a structure for designing available site content.
The Position of Cross-Browser Assessment
Cross-browser testing consists of evaluating a website’s performance and look across different website browsers (such as Chrome, Firefox, Firefox, and Edge) and even devices (like personal computers, tablets, and smartphones). This testing helps to ensure that a website gives a regular user knowledge whatever the user’s browser or device.
one. Ensuring Consistency Throughout Internet browsers
Different browsers interpret web code (HTML, CSS, JavaScript) in slightly distinct ways. This deviation can lead to be able to inconsistencies in precisely how content is shown and interacted using. Cross-browser testing determines these discrepancies, ensuring that:
Text plus Images: Content looks consistently across web browsers, maintaining readability plus visual appeal.
Styles and Design: Websites retain their planned layout and design and style, avoiding issues such as misaligned elements or perhaps distorted images.
Interactive Elements: Forms, buttons, and other interactive elements function correctly, supplying a seamless customer experience.
2. Determining Browser-Specific Concerns
Particular browsers might have exclusive quirks or bugs that affect website accessibility. For example, some browsers may well not fully support specific HTML5 or CSS3 features, which can effects the functionality associated with accessibility tools such as screen readers. Cross-browser testing helps determine and address these issues, making sure all users, including these relying on assistive technologies, can find their way and interact together with the site effectively.
three or more. Enhancing Mobile Accessibility
With the growing make use of of mobile devices, guaranteeing that websites are accessible on cell phones and tablets is essential. Cross-browser testing contains checking how websites perform on different mobile browsers plus screen sizes. This can help:
Responsive Design: Make sure the website’s receptive design adapts properly to various display screen sizes, maintaining simplicity on mobile gadgets.
Touch Interactions: Confirm that touch-based relationships (like tapping and swiping) work as intended, ensuring users using limited dexterity can easily navigate the internet site very easily.
4. Improving Performance and Load Periods
Cross-browser testing furthermore evaluates website overall performance across different web browsers and devices. Sluggish load times or perhaps performance issues could significantly impact internet accessibility, particularly regarding users with reduced internet connections or elderly devices. Testing allows optimize performance, making sure that all customers, regardless of their own browsing environment, encounter fast and trustworthy access to net content.
Challenges within Cross-Browser Assessment
Although cross-browser testing will be essential for internet accessibility, it arrives having its own fixed of challenges:
one. Browser Partage
The particular multitude of browsers and their different versions can help make testing complex. Ensuring compatibility across most possible combinations regarding browsers and the types requires considerable effort and resources.
a couple of. Diverse Device Ecosystem
Testing across a wide range associated with devices with different display screen sizes, resolutions, and operating systems brings another layer of complexity. Emulating or physically testing on numerous devices can be time-consuming and high priced.
3. Keeping Upward with Improvements
Browsers and devices frequently receive updates, which usually can introduce new features or alter existing ones. Keeping assessment procedures up-to-date with all the latest changes is important to maintaining website accessibility.
Best Techniques for Effective Cross-Browser Testing
To efficiently enhance web ease of access through cross-browser assessment, consider the following ideal practices:
1. Prioritize Key Browsers and Devices
Identify plus focus on the most commonly used internet browsers and devices among your target audience. Tools such as Google Analytics may provide insights directly into the most well-known browsers and equipment to your users.
2. Automate Testing
Influence automated testing equipment to streamline the particular process. Automation may quickly identify key issues across numerous browsers and equipment, although manual tests is still important for more refined accessibility checks.
three or more. Incorporate Accessibility Testing Tools
Use accessibility testing tools along with cross-browser testing equipment. Tools like Axe, WAVE, and Light-house can help recognize accessibility issues and ensure compliance with WCAG guidelines.
4. Extra resources
Whenever possible, involve real users, including people that have disabilities, throughout the testing procedure. Their feedback can easily provide valuable ideas into practical accessibility challenges and help refine your tests approach.
5. Frequently Update Testing Methods
Stay informed concerning changes in browser systems and accessibility specifications. Regularly update the testing procedures to be able to accommodate new functions and address rising accessibility concerns.
Conclusion
Cross-browser testing is definitely a vital element of web growth that significantly increases web accessibility. Simply by ensuring that websites perform consistently around various browsers and even devices, and by identifying and addressing browser-specific issues, cross-browser testing helps create a good inclusive web surroundings for all customers. Inspite of the challenges, adopting guidelines in cross-browser testing can prospect to a even more accessible and useful web experience, aligning together with the principles associated with web accessibility in addition to making certain everyone, regardless of their browser or device, may interact with site content effectively.
Publishing Effective Feature Data in Cucumber: Finest Practices
Cucumber is some sort of popular tool throughout the realm regarding Behavior-Driven Development (BDD), enabling teams to write tests within plain language that stakeholders can simply know. At the center of Cucumber’s operation are feature data files, which define the particular behavior of your respective app through scenarios written in Gherkin format. Writing effective characteristic files is vital intended for ensuring that checks are both clear and maintainable. This article explores ideal practices for creating feature files within Cucumber to maximize their effectiveness.
1. Understand Gherkin Syntax
Before diving in to writing feature files, it’s essential to be able to understand Gherkin, the particular language used to write them. Gherkin syntax is designed to be simple and readable, making use of keywords like Function, Scenario, Given, Whenever, Then, And, in addition to But. Here’s the quick overview involving these keywords:
Function: Describes a certain feature in the application.
Scenario: A single illustration of how typically the feature should behave.
Given: Describes typically Learn More or perhaps setup.
When: Specifies the action or even event.
Then: Details the expected outcome.
And/But: Used to add additional conditions or perhaps steps.
2. Begin with a Obvious Feature Description
The Feature keyword introduces the feature data file and may contain a new brief description involving the feature being tested. This explanation helps anyone studying the feature document understand the purpose of the assessments.
Example:
gherkin
Duplicate code
Feature: User Login
As being a signed up user
I wish to be able to log in to my account
So that I can access personalized written content
A well-defined function description sets the particular context and scope for the situations in this article.
3. Write Scenarios that Reflect Real-World Use Situations
Scenarios should represent real-world use instances or user stories. Each scenario have to test a particular aspect of the feature. Avoid excessively complex scenarios of which try to test multiple functionalities in once; instead, focus on one conduct per scenario.
Instance:
gherkin
Copy computer code
Scenario: Successful logon with valid recommendations
Given I feel for the login site
After i enter good credentials
And We click the sign in button
Then My partner and i should see typically the user dash
5. Use Descriptive Methods
Each step in the scenario should always be descriptive and simple to understand. Avoid using technical jargon or ambiguous terms. The goal is for anyone, including non-technical stakeholders, to go through and understand the feature file.
Example:
gherkin
Copy code
Presented I am around the login page
is usually clearer than:
gherkin
Copy code
Given I am about the site
five. Keep Steps Constant
Consistency in action definitions makes function files easier to be able to maintain. Use the identical phrasing and lingo across your cases. For instance, if you utilize “log in” in one scenario, avoid moving over to “sign in” in another circumstance unless there’s some sort of clear reason.
Example of this:
gherkin
Copy computer code
When I get into valid credentials
need to consistently match the particular step definitions in the step definitions data file.
6. Avoid Redundancy with Background
In the event that multiple scenarios reveal a common installation, utilize Background keyword to define actions which can be common to be able to all scenarios inside the feature. This helps avoid redundancy plus keeps your feature files DRY (Don’t Repeat Yourself).
Example:
gherkin
Copy program code
Feature: User Login
Background:
Given I am on the logon web page
Scenario: Prosperous login with legitimate qualifications
When My partner and i enter valid credentials
And I click the login button
I then should see typically the user dashboard
Situation: Unsuccessful login with invalid credentials
If I enter broken credentials
And I click on the login press button
Then I need to see an mistake message
7. Employ Tags to Organize Scenarios
Tags are helpful regarding organizing scenarios and controlling which situations are executed. An individual can tag scenarios based on their type, priority, or any other classification that suits your project.
Example:
gherkin
Copy code
@smoke
Scenario: Successful login with valid experience
Given I feel for the login page
While i enter legitimate experience
And I actually click the get access button
Then I should see the particular user dashboard
A person can run only tagged scenarios applying Cucumber’s command-line choices, which can be helpful for selective testing.
8. Include Examples for Data-Driven Testing
To check multiple variations of a scenario, employ the Examples key phrase. This allows an individual to define some sort of scenario once and run it together with different sets of data.
Example:
gherkin
Copy code
Scenario Outline: Login with various credentials
Given I actually am for the get access page
When I enter ”
And i also simply click the login button
Then I should see ”
Examples:
| username | pass word | result |
| validUser | validPass | end user dashboard |
| invalidUser | invalidPass | error concept |
9. Review and Refactor Regularly
Feature files ought to be reviewed and even refactored regularly to ensure they continue to be relevant and effective. As the application evolves, the situations will need updates to reflect new features or changes in efficiency.
Review: Regularly verify for outdated or redundant scenarios.
Refactor: Simplify scenarios in addition to remove any that no longer provide a purpose.
ten. Collaborate with Stakeholders
Finally, involve stakeholders in the procedure of writing plus reviewing feature documents. Their feedback can help ensure of which the scenarios precisely reflect the enterprise requirements and that the terminology used is apparent and even understandable.
Bottom line
Writing effective feature data files in Cucumber needs attention to quality, consistency, and collaboration. By understanding Gherkin syntax, focusing about real-world use situations, maintaining descriptive steps, and leveraging characteristics like Background, Tags, and Examples, an individual can create characteristic files that are not just functional but in addition quickly understandable by almost all team members. Normal review and stakeholder collaboration will more enhance the efficiency of your feature documents, ensuring they continue to be a very important asset through the development lifecycle.
Visual Regression Testing regarding CSS: Ensuring Steady UI
In the ever-evolving world of website development, ensuring a new consistent and creatively appealing user software (UI) is vital. As websites and even web applications grow in complexity, developers face the challenge involving maintaining visual regularity across various equipment and browsers. This particular is where image regression testing arrives into play. Particularly, visual regression tests for CSS is actually a crucial aspect associated with modern web advancement, helping to ensure that styling changes tend not to inadvertently affect the particular user experience. This article delves in to the importance involving visual regression testing for CSS, is exploring its methodologies, plus provides practical insights for implementing powerful testing strategies.
Comprehending Visual Regression Tests
Visual regression testing is a technique used to detect unintentional visual changes inside an online application or website. Unlike efficient testing, which focuses on making sure characteristics work as designed, visual regression testing concentrates on the particular appearance of the particular UI. This sort of testing identifies discrepancies between the existing version in the program and a primary version, specifically concentrating on visual elements like layout, colors, fonts, and overall style.
In the circumstance of CSS (Cascading Style Sheets), visible regression testing becomes essential because CSS is responsible for defining the particular presentation of CODE elements. Any modifications in CSS files—whether intentional or accidental—can lead to visual inconsistencies that may well impact the user expertise. Therefore, having some sort of robust visual regression testing strategy assists developers catch these types of issues before that they reach the clients.
Why Visual Regression Testing Concerns
Uniformity Across Devices and even Browsers: Modern net applications need to operate seamlessly across a multitude of devices and browsers. Visible regression testing ensures that CSS changes do not trigger layout issues or visual discrepancies on different screen sizes and browsers.
Protecting against Design Drift: After some time, minor CSS changes can accumulate plus lead to significant deviations through the original design. Visual regression assessment helps detect these gradual changes and even maintain alignment together with the design specs.
Reducing Manual Testing Efforts: Manual visual testing is time consuming and prone to human error. Automated visual regression tests streamlines the process, providing quick and accurate results.
Guaranteeing Design Integrity: With regard to businesses, maintaining a consistent and high-quality image presentation is important for brand personality. Visual regression testing helps preserve typically the integrity of design and style elements and assures that branding continues to be consistent.
Methodologies intended for Visual Regression Screening
Several methodologies in addition to tools can be used regarding visual regression testing, each having its benefits and limitations. In this article are some popular approaches:
Pixel-Perfect Comparability: This technique involves evaluating screenshots of the baseline and current versions of the software on a pixel-by-pixel basis. Tools like Percy and BackstopJS are popular options for pixel-perfect comparison. Could approach provides large accuracy, it could be sensitive in order to minor changes, this sort of as slight variations in rendering due in order to browser updates.
Layout-Based Comparison: Instead of comparing pixel-by-pixel, layout-based comparison tools focus on the structure and positioning regarding elements. These tools, for instance Applitools Eyes, detect visual adjustments in terms regarding layout as opposed to actual pixel values. This particular method is helpful for identifying layout shifts without being overly sensitive to minor rendering distinctions.
Responsive Testing: Presented the diverse variety of devices and even screen sizes, responsive testing ensures that CSS changes carry out not negatively effect the appearance upon different devices. Equipment like BrowserStack and even LambdaTest facilitate responsive visual regression testing by allowing designers to test across various device designs.
Cross-Browser Testing: Visual inconsistencies can occur as a result of differences throughout how browsers interpret CSS. Cross-browser testing tools, for example Selenium and TestCafe, help identify issues connected to browser abiliyy and ensure of which the UI remains to be consistent across different web browsers.
Putting into action Visual Regression Assessment for CSS
To effectively implement visual regression testing regarding CSS, follow these steps:
Define Baselines: Build baseline screenshots or perhaps visual representations with the UI that act as the reference stage for comparison. These types of baselines should represent the expected visible state of the application.
Select Tools: Choose the correct visual regression screening tools based on your requirements. Consider factors such as the level of accuracy needed, typically the types of aesthetic changes to detect, plus integration with your development workflow.
Handle Tests: Integrate aesthetic regression tests into your continuous integration/continuous deployment (CI/CD) pipe. Automated testing helps to ensure that visual changes usually are detected early within the development process and helps prevent regressions coming from reaching production.
Overview and Address Concerns: Analyze the outcomes of visual regression tests to discover and address any discrepancies. Review differences between the base and current variations, and determine whether they may be intentional or indicative of some sort of problem.
Maintain and Update Baselines: As the application evolves, regularly update baseline screenshots to reflect the most recent design changes. This can help maintain the relevance of visual regression tests and ensures that they carry on to provide significant feedback.
Incorporate Comments Loops: Encourage suggestions from designers and stakeholders to confirm visual changes. this contact form between developers and designers helps make sure how the visual elements align with design and style expectations.
Best Procedures for Visual Regression Testing
Give attention to Crucial UI Elements: Prioritize testing for essential UI elements that will have the most significant influence on user experience. This includes routing menus, buttons, kinds, and other online components.
Handle Active Content: Be informed of dynamic written content, such as user-created data or varying content length, that might affect visual evaluations. Configure your tests tools to manage such scenarios or perhaps exclude dynamic content material from visual reviews.
Monitor Performance: Aesthetic regression testing can be resource-intensive. Keep track of the performance regarding your testing facilities and optimize that to ensure of which tests run proficiently without causing gaps in the development pipeline.
Regularly Assessment Test Results: On a regular basis review test leads to identify patterns in addition to trends in visual discrepancies. This will help in fine-tuning typically the testing process plus addressing recurring problems.
Stay Updated along with Tools: Maintain your image regression testing tools up to time with the latest characteristics and improvements. Instrument updates may consist of enhancements in accuracy, performance, and the usage capabilities.
Bottom line
Visual regression testing with regard to CSS plays a new crucial role to maintain a consistent and even visually appealing end user interface across net applications. By finding and addressing unintended visual changes, builders can ensure that CSS modifications tend not to compromise the end user experience. Employing various methodologies and tools, integrating testing into CI/CD pipelines, in addition to following best practices contribute to successful visual regression tests. Ultimately, a well-implemented visual regression tests strategy helps produce a polished and trusted user interface of which meets both design and style specifications and consumer expectations.
CBD for Seizures in Dogs: What You Have to have to Know and How to Use It
Viewing your furry friend experience a seizure can be a terrifying encounter for any pet operator.
Seizures in canine can happen for a wide variety of factors, this sort of as epilepsy, mind tumors, or head accidents.
Though traditional medications can aid regulate seizures, lots of pet homeowners in Canada are turning to
CBD as a purely natural choice. In this posting, we'll discuss what you have to have to know about employing CBD for
seizures in pet dogs, which includes its gains, opportunity challenges, and how to use it securely.
Being familiar with CBD for Seizures in Canine
CBD, or cannabidiol, is a non-psychoactive compound uncovered in the cannabis plant. It has been
proven to have anti-inflammatory, anti-nervousness, and neuroprotective properties, producing it a promising
choice for controlling seizures in canine. CBD performs by interacting with the endocannabinoid process
(ECS) in the human body, which plays a purpose in regulating numerous bodily capabilities, such as the anxious
process.
Benefits of CBD for Seizures in Puppies
A single of the largest added benefits of CBD for seizures in dogs is its prospective to reduce the frequency and
severity of seizures. CBD has been revealed to have anticonvulsant houses, that means it can enable
minimize the activity of neurons that contribute to seizures. Additionally, CBD might help decrease
swelling in the mind, which can also lead to seizures.
Using CBD for Seizures in Dogs
If you're contemplating working with CBD to handle your canine's seizures in Canada, it's important to consult with
with a veterinarian very first. Your veterinarian can enable identify if CBD is a good possibility for your pet's
specific needs and can suggest you on the appropriate dosage and administration process.
When picking out a CBD item for your doggy, it's essential to glimpse for higher-quality, organic and natural hemp-
derived CBD that has been 3rd-party examined for purity and potency. CBD goods occur in a assortment
of types, which include oils, treats, and capsules. Whilst CBD oils are usually the most common selection, they
may perhaps not be suitable for all canine, as some might not tolerate the style or texture. CBD treats and
capsules might be a better alternative for picky eaters or canines with delicate stomachs.
Likely Challenges of CBD for Seizures in Canines
While CBD is generally considered safe for puppies, there are some prospective risks to be informed of. Some
canine may perhaps experience facet outcomes, these as drowsiness, dry mouth, or diarrhea, particularly if specified far too
large of a dose. Moreover, CBD can interact with certain medications, so it's crucial to advise
your veterinarian of any prescription drugs your puppy is having right before starting up CBD.
Overall, CBD may be a helpful software for handling seizures in pet dogs, but it ought to constantly be employed
in conjunction with a veterinarian's advice and as element of a detailed treatment prepare. By
performing carefully with your vet and checking your puppy's response, you can assist make certain that they
are obtaining the finest attainable care and therapy for their seizures.
What learn this here now suggests
Exploration on CBD for seizure administration in puppies is however in its early phases, but so considerably, the success
have been promising. A lot of pet owners have reported substantial enhancements in their dog's
seizure frequency and severity with the use of CBD.
It's significant to note that even though CBD may perhaps be a valuable addition to your pet's seizure management
prepare, it should really under no circumstances be utilized as a alternative for approved medication without the need of consulting your
veterinarian very first. Your vet can perform with you to decide the most effective procedure prepare for your canine's
unique needs.
When paying for CBD products for seizure administration, be certain to glimpse for products that are
specifically formulated for pets and produced by reliable businesses. It's also significant to observe
dosing directions carefully and commence with a lower dose before step by step raising.
In Canada, CBD is authorized for equally human and pet use, but it's crucial to obtain products and solutions from a
licensed producer and to follow any suggestions or regulations set forth by Wellbeing Canada. As with
any new supplement or medication, it's always ideal to consult with your veterinarian prior to
introducing CBD into your dog's regimen.
Conclusion
CBD might offer a natural different for taking care of seizures in canines in Canada. By doing the job closely
with your veterinarian and choosing a substantial-quality CBD product or service, you can aid aid your puppy's
general wellness and effectively-staying. Having said that, it's vital to technique CBD use with caution and do your
investigate to make certain its basic safety and usefulness for your furry close friend
Preventive steps: How to Safeguard Your web site from XSS Attack
Introduction
Cross-Site Scripting (XSS) is a new prevalent security weakness found in website applications. XSS problems occur when an attacker injects malevolent scripts into websites viewed by other users. These intrigue can steal delicate information, manipulate web site content, and carry out unauthorized actions about behalf of customers. Protecting your site from XSS episodes is crucial to making sure the security in addition to trust of your users. This informative article outlines preventive measures to guard your website from XSS attacks.
Understanding XSS Attacks
XSS attacks are labeled into three key types:
Stored XSS: Malicious scripts are permanently stored in the target server, such as in a database, and carried out whenever a end user accesses the contaminated content.
Reflected XSS: Malicious scripts are usually reflected off some sort of web server, this sort of as in a great error message or perhaps search result, plus executed immediately within the user’s browser.
DOM-based XSS: Harmful scripts are performed as a result of modifying the DOM environment within the victim’s web browser, which can take place through client-side program code.
Preventive steps
Input Validation and Sanitization
Whitelisting: Implement whitelisting to ensure that only valid and anticipated data is accepted. This involves indicating acceptable input platforms and rejecting any kind of data that does not conform.
Sanitization: Cleanse input files by removing or escaping any possibly harmful characters. Employ libraries and frameworks that offer pre-installed sanitization functions.
Outcome Development
Encode result data before object rendering it inside the web browser. This makes certain that virtually any injected scripts are treated as simple text as opposed to executable code. Utilize the appropriate encoding using the circumstance (e. g., HTML CODE, JavaScript, URL).
Content material Security Policy (CSP)
Implement a CSP to control which usually resources can end up being loaded and carried out on the website. CSP helps mitigate XSS by restricting the types of scripts, variations, as well as other content.
Example CSP policy:
plaintext
Copy code
Content-Security-Policy: default-src ‘self’; script-src ‘self’ https://trusted.cdn.com; object-src ‘none’
HTTPOnly in addition to Secure Cookies
Arranged the HttpOnly flag on cookies to prevent them by being accessed by client-side scripts. This mitigates the risk of treatment hijacking through XSS.
Use the Safe flag to assure cookies are simply transmitted over HTTPS, preventing them coming from being intercepted throughout transmission.
Avoid Inline JavaScript
Refrain from using inline JavaScript (e. g., within software tags or celebration handlers). Instead, keep all JavaScript computer code in external data files and reference them securely.
This exercise helps enforce the stricter CSP plus makes it simpler to manage and assessment JavaScript code.
Avoiding User-Generated Content
Correctly escape user-generated written content before displaying it on the website. This involves replacing characters like <, >, and & with their very own corresponding HTML agencies (<, >, & ).
Use Protection Libraries and Frames
Utilize security-focused libraries and frameworks that offer built-in defense against XSS attacks. For example, frameworks like AngularJS, Behave, and Vue. js have mechanisms to handle XSS safely and securely.
Regular Security Audits and Penetration Tests
Conduct regular security audits and transmission testing to recognize and even address potential weaknesses. Automated tools in addition to manual testing can easily help uncover XSS vulnerabilities that may possibly be missed in the course of development.
Educate Developers
Educate your enhancement team about XSS vulnerabilities and secure coding practices. Normal training sessions and workshops can support developers stay up to date for the latest safety measures trends and strategies.
Implement Web Software Firewalls (WAF)
Deploy a WAF to be able to filter and screen HTTP traffic involving your web app and the world wide web. A WAF can easily detect and block malicious requests, which includes those attempting XSS attacks.
Case Study: Real-World XSS Strike
In 2014, amazon experienced a significant XSS vulnerability of which allowed attackers to inject malicious code into product results. When my response viewed these listings, the scripts executed and redirected those to phishing websites, stealing their particular credentials. This occurrence highlighted the significance of strong XSS protection measures, including input validation, output encoding, plus CSP implementation.
Summary
Protecting your internet site through XSS attacks will be essential to sustaining the security plus integrity of your web application. Simply by implementing preventive measures this sort of as input approval, output encoding, CSP, and regular security audits, you may significantly reduce the particular risk of XSS vulnerabilities. Educating your current development team plus leveraging security libraries and frameworks even more enhances your website’s defenses. Stay aware and proactive in your security efforts to guard your users and their data from destructive attacks
Comparative Analysis: Back-to-Back Tests vs. Other Tests Methods for AI Code Generators
As AI code generators come to be increasingly integral to software development, guaranteeing their reliability and effectiveness is essential. Among the different testing methodologies employed to assess these systems, back-to-back screening is gaining popularity. This short article provides some sort of comparative analysis of back-to-back testing as opposed to other testing strategies, highlighting their strong points and weaknesses within the context associated with AI code generators.
Understanding Back-to-Back Tests
Back-to-back testing involves comparing the outcome regarding an AI signal generator with of which of your trusted origin or baseline program. The goal is to ensure that the particular AI-generated code suits the expected output when given the same input. This method is specially useful regarding validating the correctness of code generation models by benchmarking their outputs against known, reliable effects.
Pros of Back-to-Back Testing:
Direct Assessment: Provides a crystal clear and direct approach to measure the accuracy and reliability of the AI-generated computer code by comparing that into a trusted research.
Immediate Feedback: Will help in quickly figuring out discrepancies and errors between the AI-generated code and typically the baseline, allowing intended for rapid iterative improvements.
Quantitative Metrics: Helps the generation regarding quantitative metrics which you can use to assess the particular performance of various versions or iterations of the AJE model.
Cons involving Back-to-Back Testing:
Reliance on Baseline: Relies greatly on the availability and accuracy of the trusted baseline, that might not always be accessible or may itself be outdated.
Constrained Scope: Often concentrates on specific test out cases and might not really capture broader issues or edge situations that could affect the overall functionality in the AI code electrical generator.
Maintenance Overhead: Demands regular updates to the baseline to keep it relevant, including to the preservation workload.
Other Tests Techniques for AI Computer code Generation devices
While back-to-back testing is beneficial, it is far from the only method available. In this article, we explore other testing approaches in addition to compare their effectiveness to back-to-back tests.
1. Unit Tests
Unit testing involves testing individual elements or functions from the code generator in isolation to guarantee they perform because expected.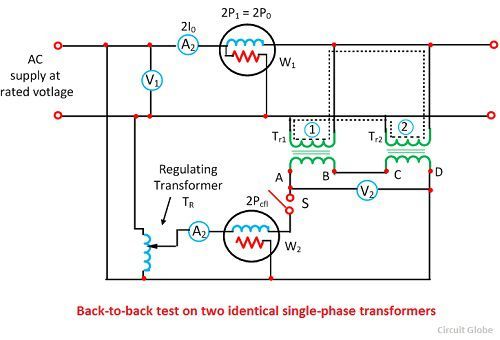
Pros:
Focused Testing: Allows for comprehensive examination of specific components or functions, improving code dependability.
Early Detection: Can be useful for identifying and repairing issues early within the development process.
Downsides:
Limited Coverage: Might not exactly fully capture incorporation or system-level concerns.
Manual Effort: Needs significant manual effort to write and even maintain test circumstances.
2. More Bonuses assesses how different elements of the AJE code generator interact, ensuring that built-in modules function appropriately overall.
Pros:
All natural View: Provides insights into how well different parts of the system interact with the other person.
System-Level Validation: Can be useful for detecting issues of which arise from the particular integration of several components.
Cons:
Complexness: Can be complex and time-consuming, particularly for large systems with numerous components.
Concern Localization: Difficult to be able to pinpoint specific parts causing issues inside integration tests.
a few. End-to-End Testing
End-to-end testing evaluates the particular entire AI program code generator’s workflow from start to finish, simulating real-world situations to assure overall features.
Pros:
Real-World Simulation: Tests the technique in a real-world context, providing the comprehensive assessment regarding functionality.
User Point of view: Reflects user experience and identifies concerns that may influence end-users.
Cons:
Resource-Intensive: Requires significant assets and setup, frequently involving extensive test out scenarios.
Complex Debugging: Difficult to debug issues due to be able to the broad scope of testing.
four. Regression Assessment
Regression testing ensures that recent changes or up-dates to the AI code generator do not adversely affect current functionalities.
Pros:
Modify Validation: Validates of which new changes do not introduce new bugs or break existing features.
Continuous Incorporation: Often integrated straight into continuous integration pipelines, enabling ongoing approval.
Cons:
Test Maintenance: Requires updating test out cases as the system evolves, which usually can be labor intensive.
Potential Overlap: Might overlap with various other testing methods, primary to redundancy.
Comparative Analysis
Scope and even Focus:
Back-to-Back Assessment: Offers a particular comparison with some sort of baseline, centering on the accuracy of generated code against identified outputs.
Unit and even Integration Testing: Concentrates on individual pieces and their communications but may not necessarily capture overall method performance.
End-to-End Assessment: Provides a thorough view of technique performance but may be resource-intensive.
Regression Assessment: Ensures that adjustments usually do not introduce fresh issues but may possibly not cover all potential integration scenarios.
Resource Requirements:
Back-to-Back Testing: Needs a reliable baseline and maintenance involving comparison data.
Product and Integration Assessment: Requires detailed check case development plus maintenance.
End-to-End Testing: High resource consumption due to substantial testing scenarios.
Regression Testing: Integrated in to continuous integration sewerlines, but requires ongoing maintenance.
Effectiveness:
Back-to-Back Testing: Effective intended for accuracy validation but may not tackle broader integration or perhaps functional issues.
Device and Integration Assessment: Effective for uncovering issues within certain components and their interactions.
End-to-End Assessment: Effective for total system validation but may be complex and even time-consuming.
Regression Screening: Effective for ensuring stability but might overlap with additional testing efforts.
Bottom line
Each testing technique has its advantages and weaknesses, and their effectiveness can vary based in the context and even specific needs involving the AI code generator. Back-to-back testing provides a centered approach for validating the accuracy of AI-generated code in opposition to a reliable baseline. On the other hand, it must be complemented by other testing procedures, such as unit, the use, end-to-end, and regression testing, to guarantee comprehensive validation involving the AI program code generator. By leveraging a combination of these methods, builders can achieve a robust and reliable assessment strategy that address various aspects associated with the AI code generation process.
Reducing Cyclomatic Complexity inside AI-Generated Code: Best Practices
Cyclomatic complexity is a software metric used to measure the intricacy of a program. That is calculated simply by counting the amount of linearly independent paths through a program’s supply code. High cyclomatic complexity indicates a plan that is hard to understand, test out, and maintain. This metric is specifically relevant in the particular context of AI-generated code, which could occasionally produce overly complicated or unoptimized signal structures. Reducing cyclomatic complexity in AI-generated code is vital regarding enhancing code good quality, maintainability, and satisfaction.
Knowing Cyclomatic Intricacy
Cyclomatic complexity is a measure of the amount of possible pathways through a plan. It is offered by the solution:
Cyclomatic Complexity
=
𝐸
−
𝑁
+
2
𝑃
Cyclomatic Complexity=E−N+2P
where:
𝐸
At the is the variety of edges in typically the control flow graph.
𝑁
N is the variety of systems in the control flow graph.
𝑃
P is the particular quantity of connected components (usually 1 regarding a single program).
High cyclomatic complexity can lead in order to several issues:
Increased Difficulty in Testing: Even more paths mean even more test cases are usually required to accomplish comprehensive coverage.
Upkeep Challenges: Complex code is harder to understand, modify, and debug.
Error-Prone Code: Elevated complexity often correlates with a better likelihood of defects.
Ideal Practices for Decreasing Cyclomatic Complexity in AI-Generated Code
Modularization
Divide and Overcome: Break down huge functions into smaller, well-defined functions. Every function should possess an individual responsibility and a limited opportunity.
Reusable Components: Motivate the use regarding reusable components and even libraries to manage common tasks, lowering the need for repetitive code.
Refactoring
Simplify Logic: Simplify complex conditional transactions by breaking all of them into simpler, smaller sized conditions.
Remove Redundancy: Identify and eliminate redundant code. AI-generated code can at times produce repetitive or perhaps unnecessary code sections.
Use of Design Patterns
Strategy Pattern: Implement the strategy pattern to deal with complex conditional common sense by encapsulating algorithms in separate courses.
Factory Pattern: Work with the factory design to manage the creation of items, reducing the complexity in object instantiation logic.
Loop Copie
Limit Nested Loops: Avoid deeply nested loops as that they significantly increase intricacy. see it here nested coils into separate capabilities or use smooth loops where possible.
Use Iterators in addition to Generators: Utilize iterators and generators in order to handle loop common sense more elegantly in addition to reduce complexity.
Successful Use of Comments and Documentation
Very clear Documentation: Ensure of which code is well-documented with clear details of complex common sense and the reason for each function.
In-line Comments: Use in-line comments judiciously to explain non-obvious parts associated with the code, helping future maintainability.
Adopt Modern Language Characteristics
Functional Programming Constructs: Use functional coding constructs like map, filter, and decrease to simplify files manipulation and minimize the particular need for specific loops and conditionals.
Pattern Matching: Make use of pattern matching functions obtainable in some modern languages to simplify conditional logic.
Automated Tools and Static Examination
Linting Resources: Use linting tools to automatically detect and suggest enhancements for complex computer code segments.
Complexity Analyzers: Employ tools of which specifically measure cyclomatic complexity and offer insights into which usually parts of the particular codebase need refactoring.
Unit Testing plus Test-Driven Development (TDD)
Comprehensive Testing: Publish unit tests for all critical elements of the computer code to ensure of which refactoring efforts do not introduce new bugs.
TDD Practices: Adopt TDD procedures to write tests before code, guaranteeing that the computer code is developed with simplicity and testability in mind.
Functional Examples
Refactoring a Complex Function:
python
Copy code
# Authentic complex function
def process_data(data):
if information is not Not one:
if isinstance(data, list):
for item within data:
if piece % 2 == 0:
print(f”Even range: item “)
different:
print(f”Odd number: item “)
elif isinstance(data, dict):
for key, value in info. items():
print(f”Key: key, Value: value “)
else:
print(“No files provided”)
# Refactored performance
def process_list(data):
for item within data:
if piece % 2 == 0:
print(f”Even number: item “)
else:
print(f”Odd number: item “)
def process_dict(data):
for key, value in data. items():
print(f”Key: key, Worth: value “)
outl process_data(data):
if information is None:
print(“No data provided”)
come back
if isinstance(data, list):
process_list(data)
elif isinstance(data, dict):
process_dict(data)
Applying Design Patterns:
python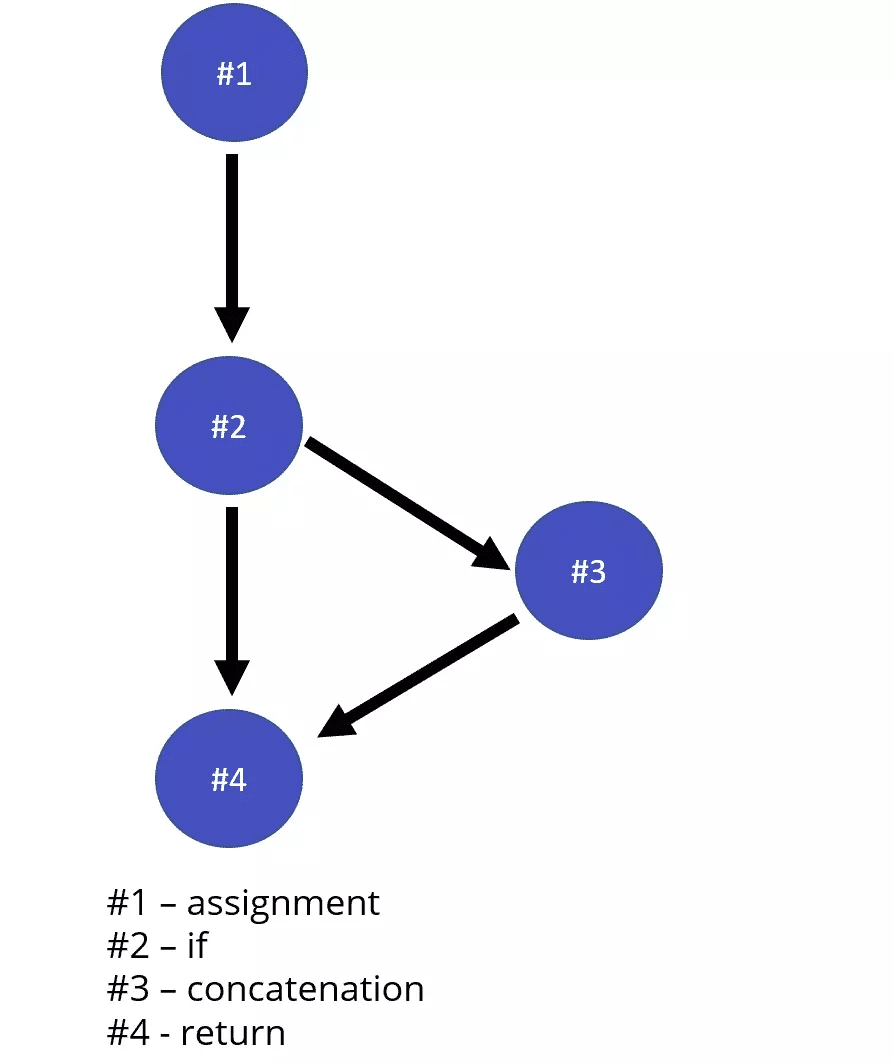
Copy code
# Strategy Pattern in order to handle different repayment methods
class PaymentStrategy:
def pay(self, amount):
pass
class CreditCardPayment(PaymentStrategy):
def pay(self, amount):
print(f”Paid amount applying Credit Card”)
school PayPalPayment(PaymentStrategy):
def pay(self, amount):
print(f”Paid amount using PayPal”)
course PaymentContext:
def __init__(self, strategy):
self. technique = strategy
def execute_payment(self, amount):
home. strategy. pay(amount)
# Client program code
payment_method = CreditCardPayment()
context = PaymentContext(payment_method)
circumstance. execute_payment(100)
Realization
Decreasing cyclomatic complexity inside AI-generated code is definitely essential for maintaining code quality, boosting maintainability, and making sure efficient testing. By adopting best practices such as modularization, refactoring, using design styles, simplifying loops, and leveraging modern dialect features, developers may significantly reduce typically the complexity with their computer code. Additionally, employing automated tools and pursuing disciplined testing practices will further support in managing in addition to mitigating the cyclomatic complexity of AI-generated code. By centering on these strategies, programmers can produce solution, more maintainable, and even robust code, ultimately bringing about more effective and sustainable software program projects
Typically the Role of AJE in Automating BDD Scenarios: Tools plus Techniques
In the speedily evolving field society development, Behavior-Driven Enhancement (BDD) has appeared as a popular methodology for enhancing collaboration between specialized and non-technical team members. BDD centers on defining clear, understandable requirements by means of user stories and scenarios, fostering better communication and making sure alignment between stakeholders. However, as assignments grow in complexness, manually managing plus executing these situations may become cumbersome. This is where Unnatural Intelligence (AI) comes into play, offering transformative alternatives for automating BDD scenarios. This content explores the role of AI throughout this domain, highlighting key tools and even techniques that are reshaping the landscape of automated testing.
Understanding BDD and its particular Challenges
Behavior-Driven Development is definitely a methodology that emphasizes writing test out scenarios in all-natural language, which may be understood by simply all stakeholders. These kinds of scenarios, written inside a format generally known as Given-When-Then, describe specific behaviors and anticipated outcomes of typically the system. While BDD promotes clear communication and alignment, that can present various challenges:
Scalability: Since the number regarding scenarios grows, handling and executing all of them manually becomes increasingly difficult.
Maintenance: Changes in requirements often necessitate updates to scenarios, that can be time-consuming and error-prone.
Integration: Ensuring that BDD scenarios are built-in with continuous integration/continuous deployment (CI/CD) sewerlines can be challenging.
AI has typically the potential to tackle these challenges simply by automating the design, execution, and preservation of BDD scenarios.
AI-Driven Tools regarding Automating BDD Cases
Several AI-powered resources and platforms have got emerged to reduces costs of the automation of BDD scenarios. These tools leverage device learning, natural terminology processing (NLP), plus other AI methods to enhance the productivity and effectiveness associated with BDD practices.
a single. Natural Language Running (NLP) Tools
NLP plays a essential role in interpretation and converting all-natural language scenarios directly into executable test intrigue. AI-driven NLP equipment can analyze user stories and cases written in plain language and produce corresponding test circumstances automatically. Some prominent NLP tools applied in BDD automation include:
CucumberStudio: A good AI-enhanced version regarding Cucumber, CucumberStudio utilizes NLP to support in the creation and management of BDD scenarios. It allows users to publish scenarios in organic language and after that translates these into automatic tests.
Testim: Testim combines AI together with NLP to create plus maintain automated testing based on BDD scenarios. Its clever AI engine continually learns and gets used to to changes inside the application, bettering test reliability.
2. AI-Powered Test Software Frameworks
AI-powered test out automation frameworks provide advanced capabilities regarding executing and managing BDD scenarios. These kinds of frameworks utilize AJE to optimize analyze execution and increase test coverage.
Test. ai: Test. aje employs machine finding out how to automatically create plus execute tests depending on BDD scenarios. That analyzes application terme and adapts to be able to changes, reducing the advantages of manual updates.
Functionize: Functionize leverages AJE to automate the particular creation and performance of BDD cases. Its intelligent test automation platform makes use of machine learning to understand application behavior and adjust assessments accordingly.
3. Computerized Test Generation Equipment
Automated test era tools use AI algorithms to quickly generate test instances from BDD cases. They can assist in creating complete test suites by simply analyzing scenarios and identifying edge cases.
Model-Based Testing Equipment: Tools like TestCraft and TestComplete work with model-based testing strategies, where AI models analyze BDD cases to generate and even execute tests. They are capable involving covering various cases, including edge cases, by leveraging AI-based analysis.
DeepTest: DeepTest is an sophisticated tool that utilizes deep learning approaches to generate test cases from BDD scenarios. It might take care of complex test generation tasks and adjust to changes throughout the application below test.
Techniques for Applying AI in BDD Automation
Integrating AJE into BDD motorisation involves several important techniques that improve the efficiency and even accuracy of computerized testing.
1. Circumstance Analysis and Search engine optimization
AI techniques could analyze BDD scenarios to identify unnecessary or overlapping checks. By optimizing analyze scenarios, AI assists in reducing typically the overall number regarding tests while maintaining comprehensive coverage. This kind of process involves:
Clustering Algorithms: Using clustering algorithms to party similar scenarios and eliminate redundancies.
Design Recognition: Employing design recognition to recognize common test designs and optimize analyze execution.
2. Self-Healing Tests
AI-powered resources can incorporate self-healing capabilities, which allow automated tests in order to conform to changes within the application lacking manual intervention. Techniques for self-healing include:
Image AI: Leveraging visible AI to identify changes in typically the user interface plus adjust test pièce accordingly.
Behavior Research: Analyzing application conduct patterns to instantly update test circumstances in response to changes.
3. Predictive Analytics
AI can easily utilize predictive analytics to forecast potential issues and test coverage gaps. By simply analyzing historical test data and software metrics, AI-driven resources can predict locations that are likely to encounter issues, allowing teams to proactively address them.
Risk Assessment: Using predictive models to examine the risk of failure inside specific scenarios plus prioritize testing work.
Coverage Analysis: Inspecting test coverage to identify areas along with insufficient testing plus enhance overall test out suite effectiveness.
Challenges and Concerns
While AI offers substantial advantages for automating BDD scenarios, there are some challenges and things to consider to keep throughout mind:
Complexity involving Integration: Integrating AI tools with present testing frameworks plus CI/CD pipelines may require significant effort plus expertise.
Data Quality: AI tools depend on high-quality data regarding training and research. Ensuring that the particular data employed for education is accurate and representative is essential regarding the effectiveness regarding AI-driven automation.
Servicing and Updates: AI models require regular updates and upkeep to stay relevant and even effective. Continuous supervising and adjustment will be necessary to make sure that AJE tools adapt to adjustments in the app and testing specifications.
Conclusion
AI is revolutionizing the method BDD scenarios usually are automated, offering powerful tools and techniques that enhance performance, accuracy, and scalability. By leveraging NLP, AI-powered test software frameworks, and automated test generation tools, teams can streamline the process involving creating, executing, and even maintaining BDD scenarios. However, have a peek at these guys of AI inside BDD automation requires consideration of incorporation, data quality, and ongoing maintenance. Because AI technology continues to advance, their role in BDD automation may turn out to be even more significant, driving further improvements in software tests and quality peace of mind.
Case Study: Successful BDD Setup in AI-Powered Software Projects
In the realm of software advancement, Behavior-Driven Development (BDD) has emerged while a prominent method, particularly when placed on complex domains such as artificial intelligence (AI). BDD emphasizes cooperation between developers, testers, and business stakeholders, aiming to enhance understanding and guarantee that software delivers the desired outcomes. This article is exploring a prosperous implementation of BDD in AI-powered software projects via a detailed situation study, demonstrating their benefits, challenges, and overall impact.
Background
Company Profile:
The case study focuses in TechnoVision, a mid-sized software development company focusing on AI alternatives. TechnoVision’s portfolio includes AI-driven applications throughout healthcare, finance, plus retail. In reply to growing customer demands and more and more complex projects, the organization sought a even more efficient development strategy to align technological deliverables with company objectives.
Project Overview:

The project under review involves the development of an AI-based predictive stats platform for a new large retail customer. The platform’s aim was to analyze consumer behavior and even forecast inventory has to optimize stock ranges and reduce wastage. The project necessary extensive collaboration involving data scientists, builders, business analysts, and even the client’s stakeholders.
Initial Problems
TechnoVision faced several challenges prior to implementing BDD:
Misalignment involving Expectations: Traditional growth methodologies led to be able to frequent misunderstandings between stakeholders plus the technical team regarding project requirements and predicted outcomes.
Communication Spaces: The complex character of AI jobs often ended in fragmented communication, with technical jargon creating limitations between developers and even non-technical stakeholders.
Testing Difficulties: Making certain AI models met organization requirements was demanding due to typically the unpredictable nature of machine learning methods.
BDD Adoption
Throughout light of these problems, TechnoVision chose to carry out BDD to boost clarity, collaboration, and assessment efficiency. The ownership process involved a number of key steps:
a single. Training and Onboarding:
TechnoVision initiated thorough BDD working out for the team members, which includes developers, testers, and business analysts. Ideal to start focused on typically the principles of BDD, including writing end user stories, creating acceptance criteria, and taking advantage of equipment such as Cucumber and SpecFlow.
a couple of. Defining User Tales:
The team collaborated using the client to define clear and even actionable user stories. Each story centered on specific business outcomes, such as “As a store office manager, I want in order to receive automated inventory alerts so that My partner and i can avoid stockouts and overstocking. ”
3. Creating Popularity Criteria:
Acceptance criteria were formulated in line with the user stories. By way of example, an acceptance criterion for the supply alert feature may possibly be, “Given that will the current inventory level is under the threshold, when typically the daily report will be generated, then the alert should be sent in order to the store supervisor. ”
4. Applying BDD Tools:
TechnoVision integrated BDD resources like Cucumber within their development pipeline. These tools enabled the crew to write tests in plain language of which could be easily understood by non-technical stakeholders. The scenarios written in Gherkin syntax (e. g., “Given, ” “When, ” “Then”) had been then automated to make certain the software achieved the defined conditions.
5. Continuous Effort:
Regular workshops plus meetings were founded to make sure ongoing effort between developers, testers, and business stakeholders. This method helped deal with issues early and kept the job aligned with company goals.
Successful Setup
The BDD approach led to several good outcomes in the particular AI-powered project:
one. Enhanced Communication:
BDD’s use of simple language for determining requirements bridged typically the communication gap between technical and non-technical team members. Stakeholders could now understand and validate requirements and even test scenarios a lot more effectively.
2. Increased Requirement Clarity:
Simply by focusing on company outcomes rather compared to technical details, the particular team was able to assure that the produced AI models aligned with the client’s expectations. This strategy minimized the risk of range creep and imbalance.
3. Efficient Tests:
Automated BDD assessments provided continuous suggestions on the AI system’s performance. This kind of proactive approach in order to testing helped recognize and address issues related to model accuracy and prediction top quality early in the particular development cycle.
5. Increased Stakeholder Pleasure:
The iterative and collaborative nature involving BDD ensured of which stakeholders remained engaged throughout the task. Regular demonstrations in the AI system’s functions and alignment with business goals fostered a positive partnership between TechnoVision and even the client.
5. Faster Delivery:
With clear requirements and automated testing throughout place, TechnoVision could deliver the predictive analytics platform upon schedule. The streamlined development process lead in a more efficient project lifecycle and reduced period to market.
best site . Early on Involvement of Stakeholders:
Engaging stakeholders from the outset is usually crucial for defining clear and actionable customer stories. Their engagement ensures that the particular project stays aligned with business aims and reduces the chance of misunderstandings.
2. Constant Feedback:
Regular feedback loops are necessary for maintaining position between business needs and technical giveaways. BDD facilitates this by integrating stakeholder feedback into the particular development process by way of automated tests in addition to user stories.
three or more. Training and Assistance:
Investing in BDD training for the entire team is definitely vital for successful implementation. Comprehensive training helps team users understand BDD concepts and tools, top to more efficient cooperation and project final results.
4. Adaptability:
Whilst BDD is a highly effective methodology, you should adapt it towards the specific needs of AJE projects. The iterative nature of AJE development requires versatility in defining consumer stories and approval criteria.
Bottom line
TechnoVision’s successful implementation regarding BDD inside their AI-powered predictive analytics job demonstrates the methodology’s effectiveness in handling common challenges in software development. By simply fostering better connection, clarifying requirements, and even improving testing productivity, BDD written for the project’s success and even enhanced stakeholder satisfaction. The lessons discovered from this situation study provide beneficial insights for some other organizations aiming to adopt BDD in complex, AI-driven projects.
By means of collaborative efforts and even a focus about business outcomes, TechnoVision exemplifies how BDD may be leveraged to achieve success inside the rapidly evolving field of AI.


